How To Configure SSH Keys Authentication With PuTTY And Linux Server
This tutorial explains how you can replace password-based SSH authentication with key-based authentication which is more secure because only the people that own the key can log in. In this example, we're using PuTTY as our SSH client on a Windows system.
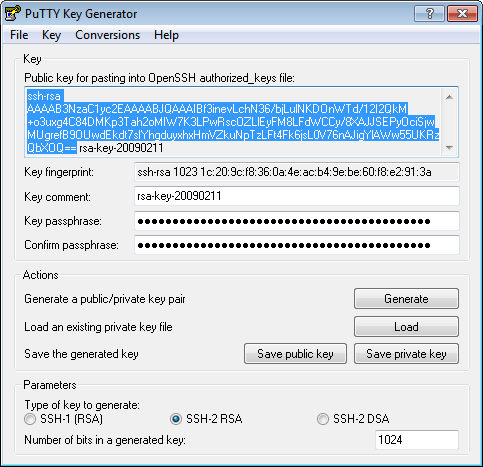
Generate a private and public key pair
Open PuTTYgen.exe, press Generate button, move mouse. Once the keys are generated, type your key passphrase (choose a «hard to guess» one). Save Public key. Save Private key.
Configure your Linux server (create user, save public key)
For this guide let's assume you regular login name is us3r (replace it with one that you use regularly).
As root, on the shell, type:
adduser us3r --disabled-password
You will be asked to fill in some details such as the user's real name (empty string is fine).
Now type:
su us3r cd /home/us3r mkdir .ssh chmod 700 .ssh cd .ssh
Then in that folder, create and edit a file called authorized_keys2.
In there, cut/paste your public ssh key, on ONE LINE (That is very important!!!)
- Do not add the email@example.com at the end of the line.
- Do not add the BEGIN PUBLIC KEY or END PUBLIC KEY.
- Do not add the rsa-key-20090211 at the end.
- Make sure, there is ssh-rsa at the beginning.
It should be something like:
ssh-rsa AAAAB3NzaC1yc2EAAAABJQAAAIBf3inevLchN36/bjLulNKDOnWTd/12I2QkM+o3uxg4C…
Type:
chmod 600 authorized_keys2
Add Private key to PuTTY SSH authentication agent
Start the PuTTY SSH authentication agent PAGEANT.EXE. When started, right-click its systray icon and select «add key». Select your private key file, and type in your passphrase when you add the key. The Pageant works as a passphrase keeper.
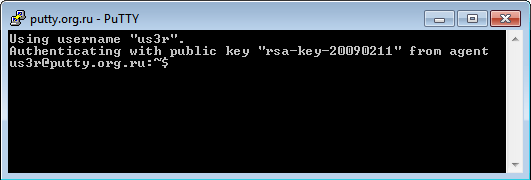
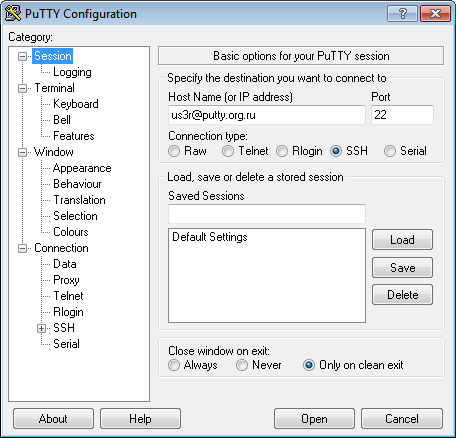
Use PuTTY to connect to your server
Open PuTTY and connect as us3r@putty.org.ru:
See that you log in without a password …